Customer Key Management (BYOK)
OpenNVR adheres to strict zero-trust principles. By default, you should assume that the physical hardware OpenNVR runs on could be compromised, stolen, or seized.
To mitigate physical extraction, the platform implements a permanent Bring Your Own Key (BYOK) cryptographic architecture. All critical metadata, AI inference responses, and long-term recording fragments are encrypted at rest using your own mandated AES-256 or Fernet symmetric keys.
What BYOK gives you
- Zero Phone-Home Execution: OpenNVR operates in a permanent offline-first capacity. Your cryptographic keys are never beamed to a cloud license server or externally backed up. You retain full control over the encryption lifecycle.
- Immediate Application: The moment a key is struck in the interface, the FastAPI backend applies the cryptographic salt instantaneously to all future disk writes.
- Useless without the key: Without the correct configured key, extracting the PostgreSQL database or the Docker recording volume yields perfectly randomized, useless byte streams.
Generating and Governing Keys
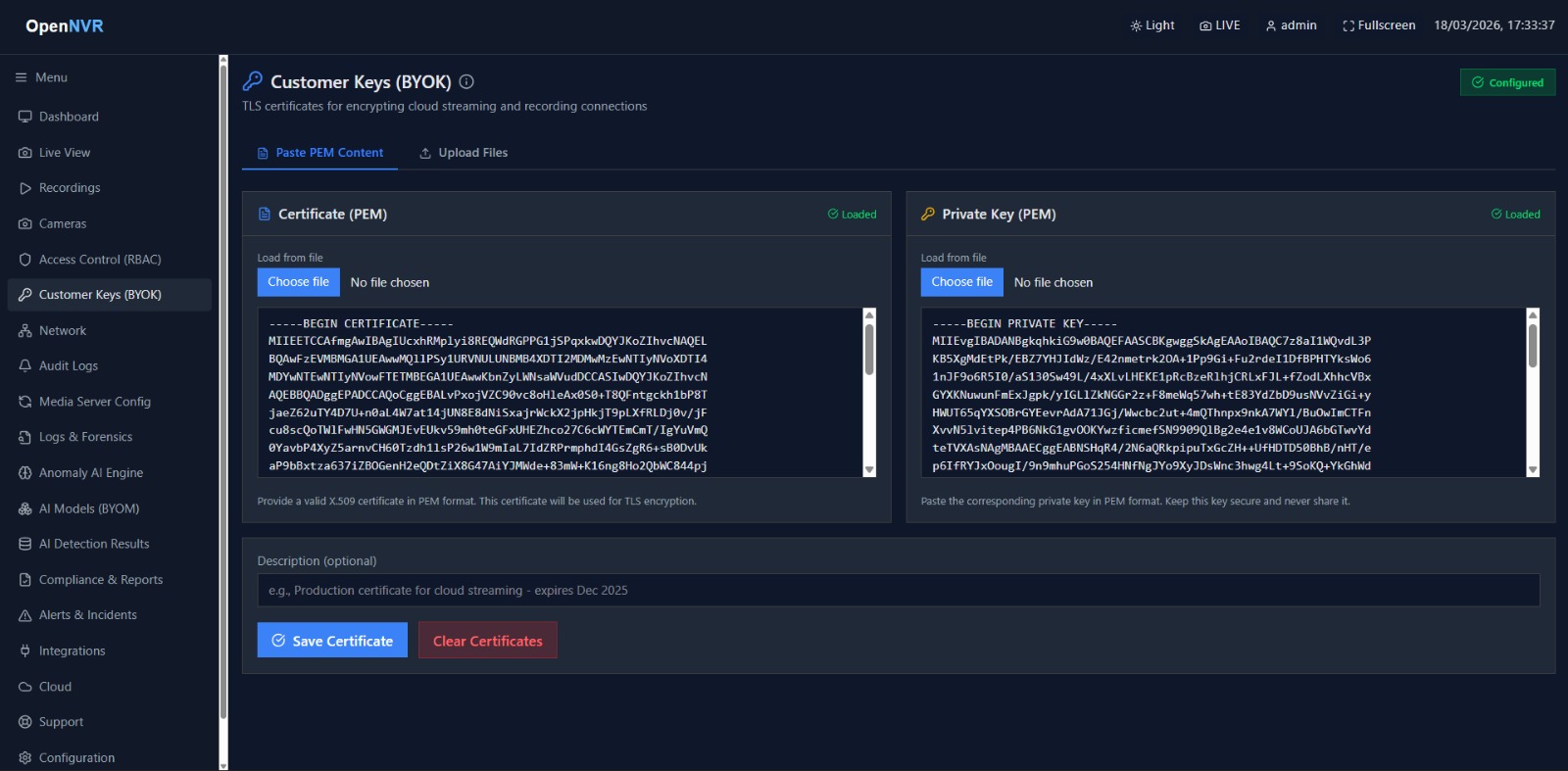
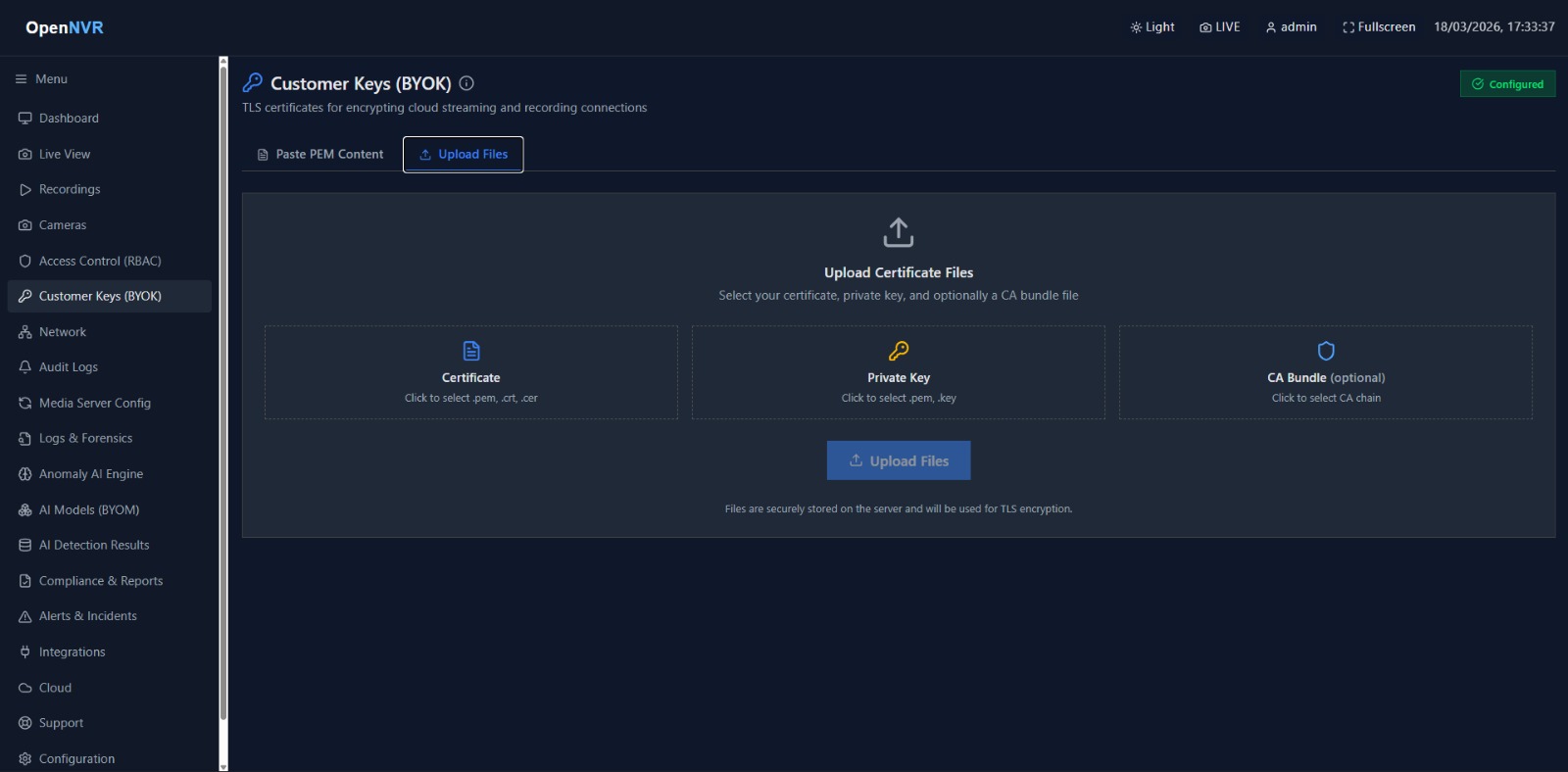
Administration of the unified key natively occurs inside the UI, ensuring you never have to blindly edit .env files with raw byte-strings.
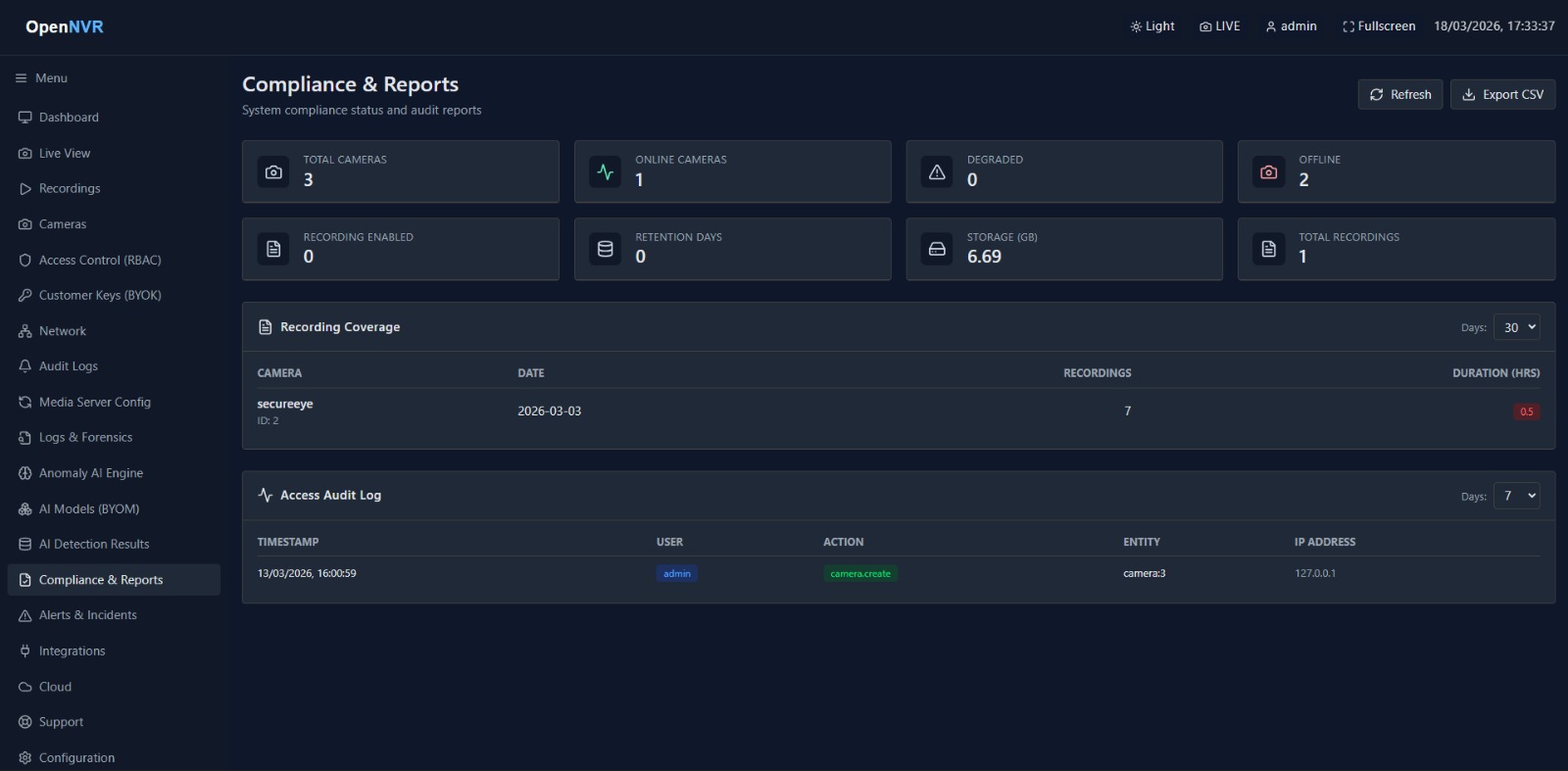
- Navigate to the Compliance & BYOK panel inside the OpenNVR Dashboard.
- Select Generate New Key to allow the system to securely cast a new high-entropy string, OR select Import Key to paste an existing strict standard AES key generated by your enterprise Hardware Security Module (HSM).
- Save and Deploy.
Strict Rotation Principles
If an employee leaves or a subnet is breached, standard security postures require key rotation.
- Safe Rotation: Schedule rotations during low-traffic retention windows.
- Legacy Playback Validation: When a key is swapped, older recordings encrypted with the previous key will remain readable only if your legacy key traces remain actively mapped in the backend keystore.
- The Golden Rule: Maintain offline hard-copies of your active keys (e.g., inside an isolated password manager or physical vault). If you lose the active key, the encrypted data is permanently, irreversibly erased by design.