User Governance & RBAC
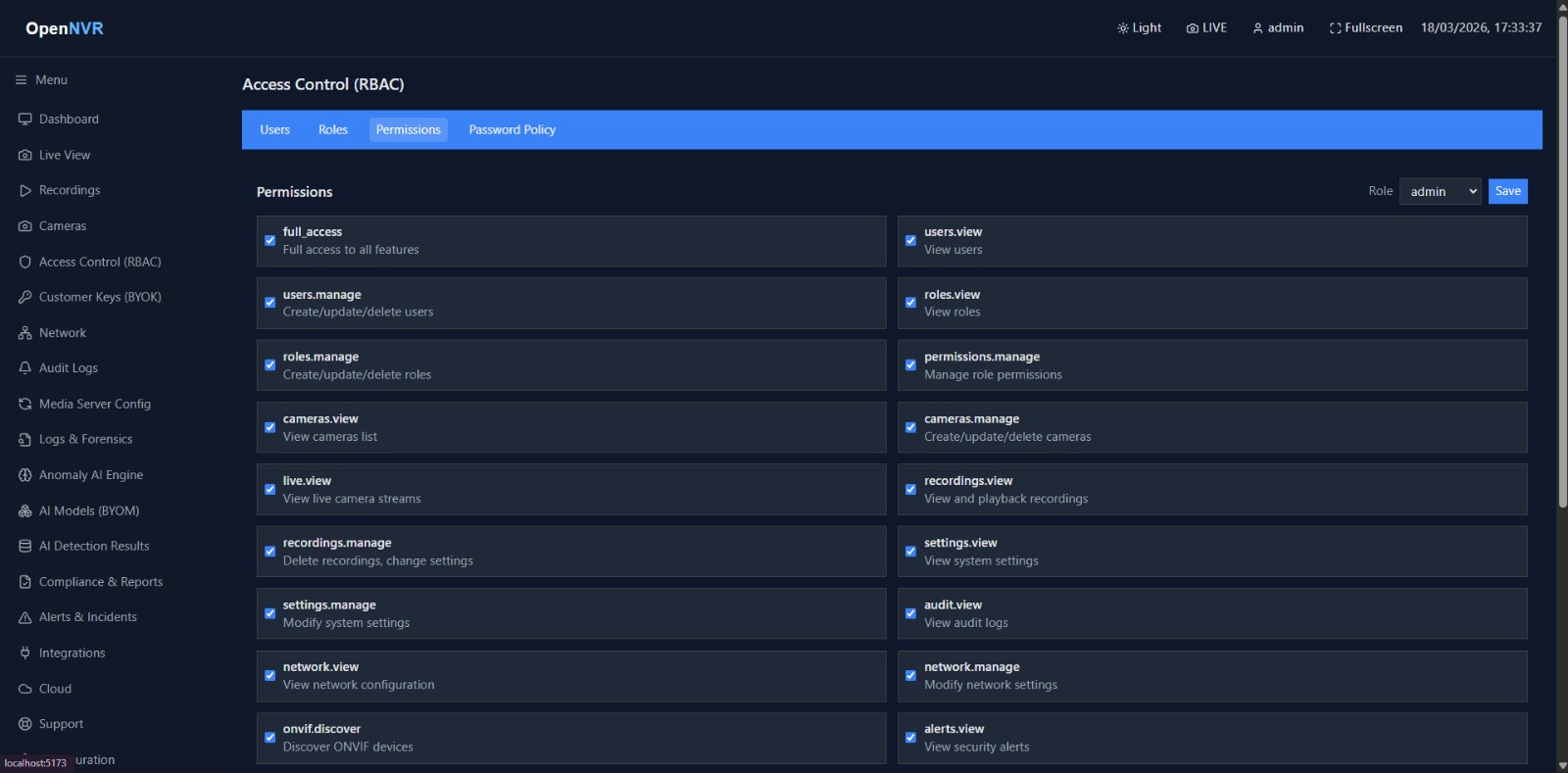
Enterprise surveillance mandates strict principle-of-least-privilege access. OpenNVR actively abandons single-admin monolithic structures in favor of a highly specialized Roles-Based Access Control (RBAC) matrix.
The RBAC Matrix
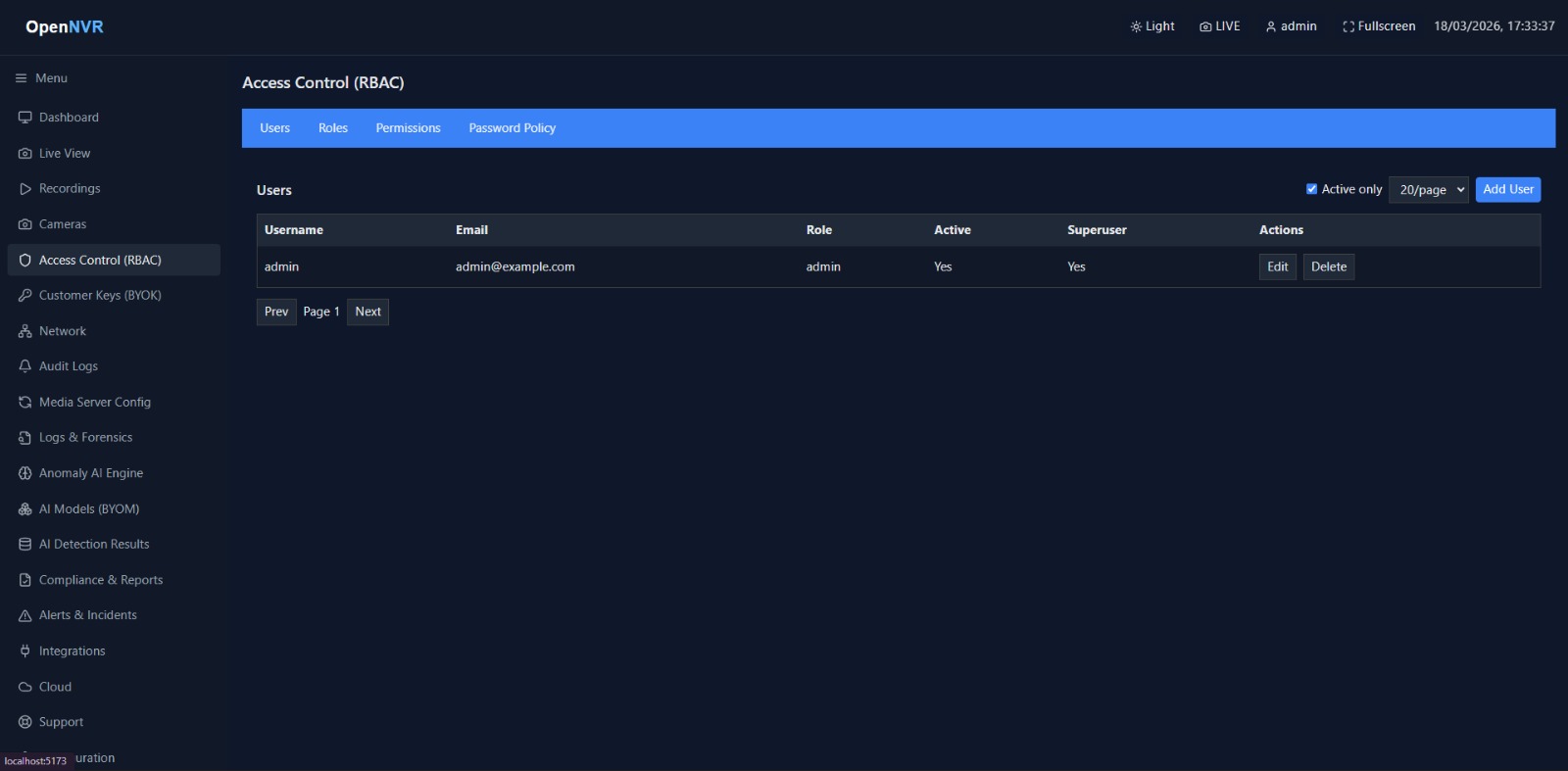
By navigating to the User Management panel within the dashboard, core administrators can explicitly carve out permissions for their downstream staff.
- Global Administrators: Possess full write privileges across the platform. Capable of mutating external AI adapter hooks, rotating BYOK encryption keys, and destroying logical volumes.
- Security Operators: Restricted to non-destructive actions. They are permitted to view real-time WebRTC streams, scrub historical HLS timelines, and export incident footage, but they cannot delete active cameras or manipulate inference pipelines.
- Auditors (Read-Only): Highly restricted governance profiles capable of parsing the system’s internal Audit Logs and Compliance metrics to generate regulatory reports, strictly isolated from manipulating the recording logic.
Enforcing Password Strategies
The NVR engine inherently trusts local users. Therefore, weak passwords act as the primary vector for internal lateral compromise. To harden the perimeter, OpenNVR allows you to mandate cryptographic complexity globally.
Within the Security Policies dashboard, you can strictly enforce:
- Minimum character lengths (e.g.,
16 charactersfor NIST compliance). - Specialized character inclusion (
Symbols,Alphanumeric mixes). - Mandatory hardware Token MFA (Multi-Factor Authentication) implementation for all new generic accounts.
- Active account lockouts (default 180 seconds) to mitigate brute-force credential stuffing.
[!WARNING] If a Global Administrator loses their MFA device or forgets their password, recovering access natively requires console-level interaction with the PostgreSQL instance to nullify the hashed vault entries.